Microsoft has moved OneLake security to general availability, and it's worth pausing on what that actually means. This isn't a new permissions UI bolted onto Fabric. It's an access control model baked into the storage layer itself — one designed to travel with the data, whether someone's hitting it from a Spark notebook, a Power BI report, a Fabric data agent, or — where supported — connections from apps like Excel.
If you've spent any time stitching together row-level security across different engines, you know why that's a big deal.
What OneLake security actually does
The model is fine-grained and role-based. You can secure data at the item, folder, table, or row/column level, and those rules apply consistently across supported Fabric engines. A user with restricted access to certain rows sees the same restriction whether they're running a notebook, opening a report, or pulling the data through the SQL Analytics Endpoint.
That last point — consistency across engines — is the interesting one. Historically, lake security has been an engine-by-engine problem: define one set of rules in your warehouse, another in your BI tool, a third for ad-hoc Spark access, and hope they stay aligned. OneLake security collapses that into a single model attached to the data. Microsoft frames this as interoperability rather than just security, and the accompanying whitepaper, The Future of Data Security is Interoperability, goes deeper into the design philosophy.
One thing worth flagging up front: workspace Admins, Members, and Contributors bypass RLS and CLS by default. That's by design — these roles are assumed to need full access for development and troubleshooting — but it means you'll want to test new policies with a Viewer account if you want to actually see them in action.
How the GA rollout works
If you're already in Fabric, this rollout is going to touch your tenant whether you opt in or not. Starting with the GA announcement, every newly created supported item has OneLake security enabled by default. Existing items can be opted in individually for now, but Microsoft will automatically upgrade all supported items over the coming weeks, with the rollout completing by the end of May.
The important caveat: this change doesn't alter existing user permissions or data access. It just enables the new role-management surface across your estate. Nothing breaks; you simply gain the ability to start authoring OneLake security roles where you couldn't before. Worth flagging to your governance and platform teams now, though, so the upgrade isn't a surprise when someone notices new options in the portal.
What's new at GA
The GA release pulls in several improvements that landed during preview, plus some fresh ones aimed at making role management less error-prone.
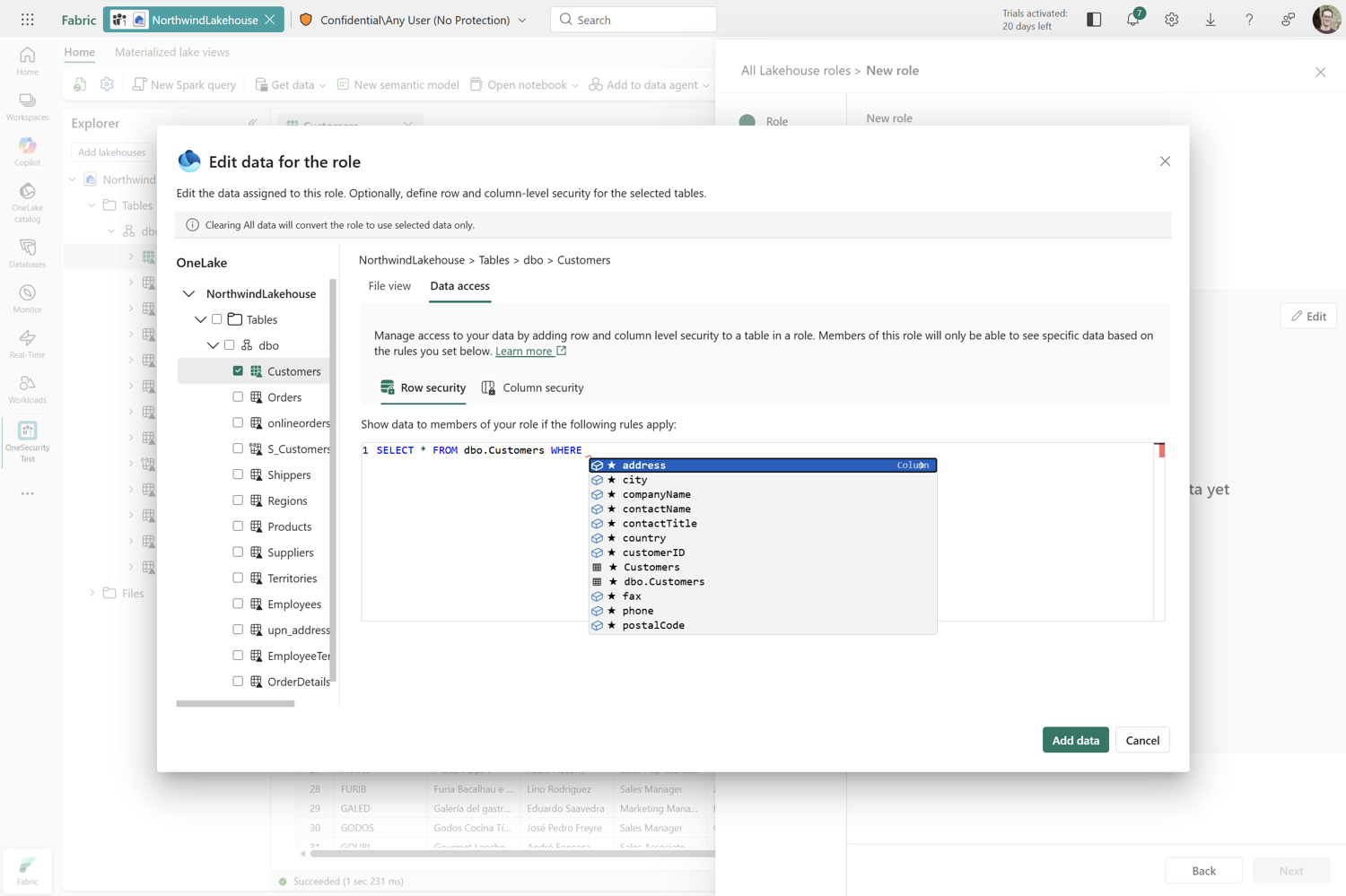
The role creation experience has been rebuilt as a wizard-style flow that walks you through each step, and crucially, lets you author both row-level security (RLS) and column-level security (CLS) policies at the point of creation. Previously you'd create the role, then circle back to layer on the security rules — an order of operations that made it easy to ship incomplete roles. Now they're complete from the start.
RLS authoring also gets inline validation and improved auto-recommendations. RLS expressions are powerful but unforgiving; small mistakes can silently misroute access or send you down a troubleshooting rabbit hole. Catching those issues during authoring rather than during a confused user's support ticket is a meaningful quality-of-life improvement.
A handful of other fixes round out the release: cross-region shortcuts are now supported, viewer permission is no longer required to share specific items, workspace private link works across all workloads except Power BI, and User's identity mode is the default for newly created SQL Analytics Endpoints.
What you may have missed during preview
A few capabilities that landed earlier are worth highlighting now that the platform is GA.
There's a set of granular REST APIs for managing individual roles, which matters if you're treating security as code or wiring role management into CI/CD. The API reference sits under the Fabric core documentation. OneLake security also extends to Mirrored Databases, so if you're using OneLake mirroring to bring data from external systems into a single Fabric estate, you can centrally govern that data with the same model. And ReadWrite permissions let you give users safe write access to OneLake — useful for collaborative scenarios where read-only is too restrictive but full ownership is too much.
Why this matters beyond Fabric
The broader story here is about where data security is heading. The traditional model — every engine implements its own permissions and we hope the rules match — doesn't scale to the multi-engine, multi-tool reality most organisations actually operate in. Attaching security to the data, in the storage layer, and having every engine respect it consistently, is the architectural shift. OneLake security is one of the more concrete examples of that idea shipping in production.
For European organisations especially, where data residency, GDPR, and sector-specific compliance regimes mean security misalignments aren't just operational headaches but regulatory ones, a single, portable access model is more than convenience. It's the difference between defensible data governance and a permissions matrix nobody fully understands. It's also the kind of topic the data and governance crowd at ECS tends to chew on for hours over coffee — interoperability is one of those quiet themes that keeps surfacing across the Fabric, security, and architecture tracks.